Connect with Customers.
Disconnect from Risks.
ThreatSTOP Platform
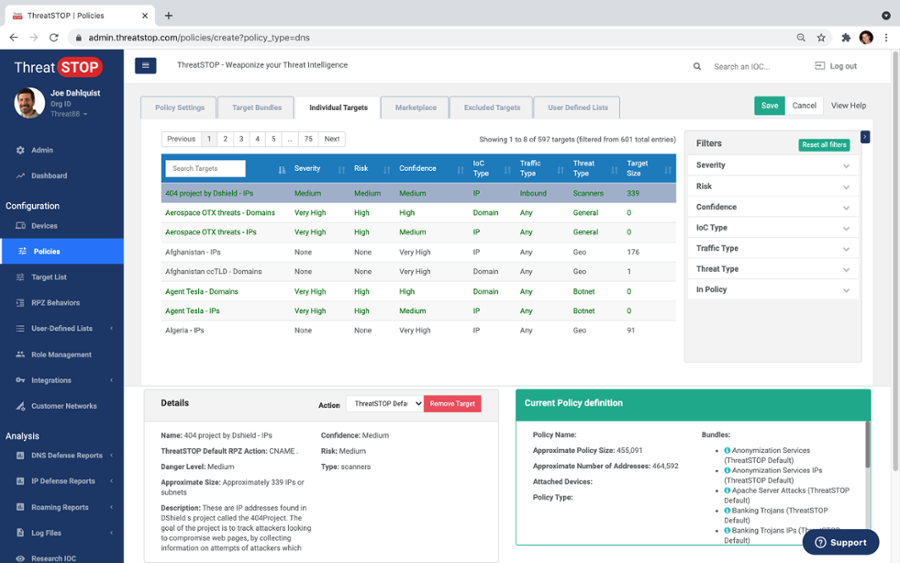
The ThreatSTOP Platform is a Web-based SaaS security platform with modular product offerings for Protective DNS (PDNS), Firewall automation, and other Threat Intel use cases.
It integrates with physical, virtual, and hosted security stack components including firewalls, DNS servers, IDPS, SIEM, etc.
The platform automates threat intelligence acquisition, curation, and timely application for threat mitigation and visibility.
- It proactively identifies and blocks all malicious network communications by tracking attacker infrastructure
- ThreatSTOP tracks 25+ Million active IOCs across hundreds of curated threat intelligence feeds on the platform, with an average (12mo) FP rate of 0.002%
- The service is compatible with virtually all popular firewalls, routers, switches, DNS servers, IDPS
- Customers typically see an immediate 80% reduction in malware infections after a 30-minute deployment


Save Time
- Automate and outsource essential 24/7 security policy updates.
- Rich reports in our portal or your SIEM.
- Rapidly identify infected hosts.
- Research tools, like Check IOC, included.
- Customize and schedule email reports and alerts.
Save Money
- Add powerful security to existing devices.
- Reduce endpoint infections and stop breaches.
- Reduce load on existing security layers.
- Eliminate unwanted bandwidth usage.
- Increase security and network efficiency.
Secure your Workforce
- Block connection attempts to criminal infrastructure on all ports and protocols.
- Continuous, automatic policy updates.
- Unique and valuable telemetry for SOC's and MSP's.
- Customize policies to match security postures.
- Multivendor security is always a feature, not a bug
Deploying ThreatSTOP
We're vendor neutral and comprehensive, with complementary Protective DNS and IP filtering. You have the ability to provision your devices and enterprise consistently, with multi-layered security.
Boundless Protection
We work everywhere. Whether your workforce is on your corporate network or working from home, we have them protected.
Tailored to your Business
Mix and match threat intelligence protection bundles based on your organization's needs, or create your own custom policies.
Seamless Integration
Device integration is fast, easy and diverse. ThreatSTOP integrates with firewalls, routers, switches, DNS servers (and more) in less than one hour.
Deploying ThreatSTOP
We're vendor neutral and comprehensive, with complementary Protective DNS and IP filtering. You have the ability to provision your devices and enterprise consistently, with multi-layered security.
Boundless Protection
We work everywhere. Whether your workforce is on your corporate network or working from home, we have them protected.
Tailored to your Business
Mix and match threat intelligence protection bundles based on your organization's needs, or create your own custom policies.
Seamless Integration
Device integration is fast, easy and diverse. ThreatSTOP integrates with firewalls, routers, switches, DNS servers (and more) in less than one hour.
ThreatSTOP has eliminated manual blacklisting and remediation, and reduced help desk tickets related to malware by 90%, to only 1-2 per month.
